DonorPoint is proud to announce that, for the EIGHTH consecutive year, we have been independently verified to be PCI-DSS Compliant in 2023! Additionally, we have a regularly-updated data security protocol, as well as reporting and detection plans in place.
—————————————————————————————————————————————————————-
How can you ensure that your vendors are as careful with their data as you are with yours?
As the recent Las Vegas hotel cyberattacks have shown, organizations of all kinds need to be vigilant about their data security — as well as making sure that any third-party vendors with access to their data are compliant as well.
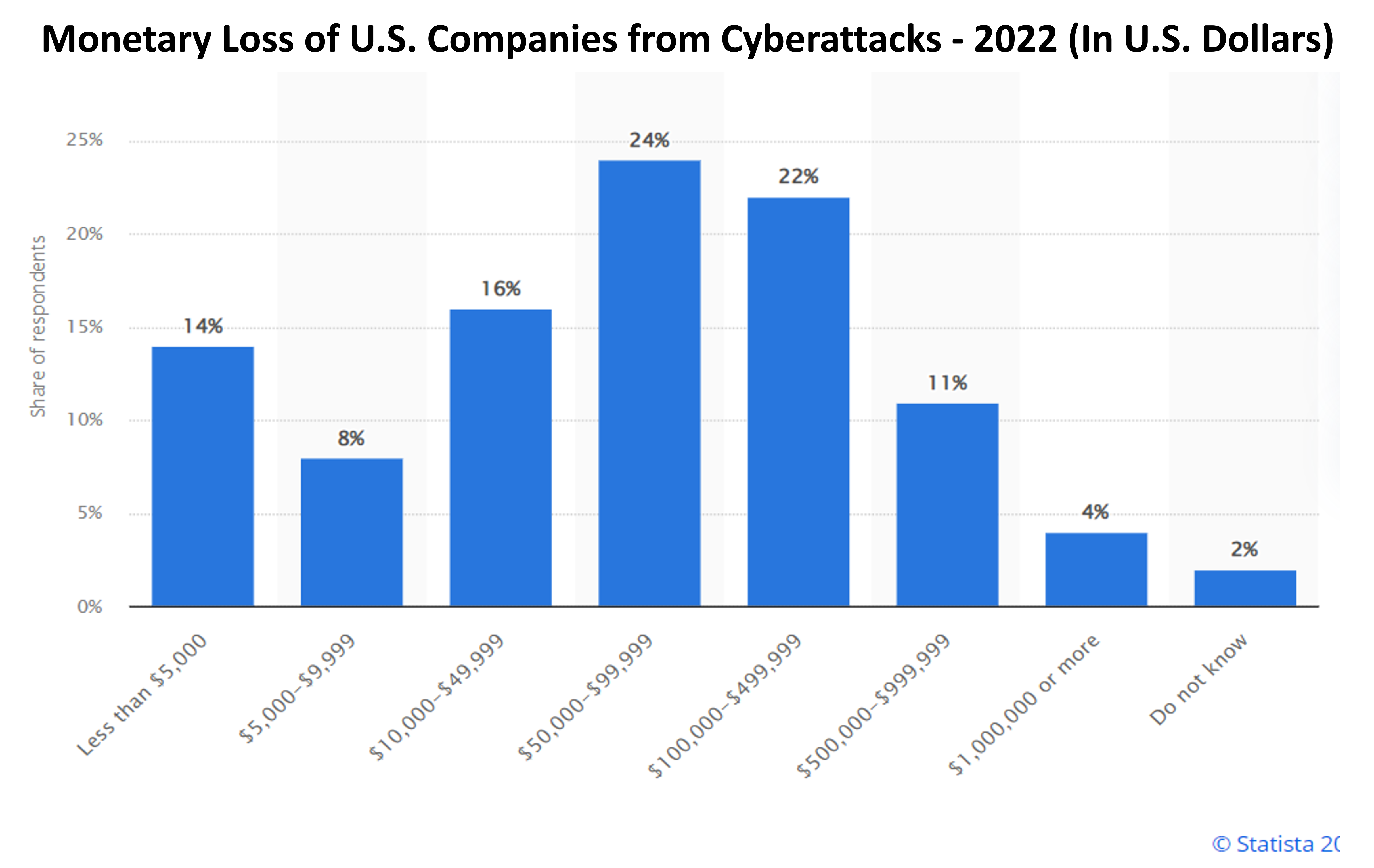
In 2022, cyberattacks reported to the FBI, while fewer in number versus the previous year, were higher in cost, with victims losing a record $10.3B. Phishing remains the most commonly reported cybercrime (by far), with business email compromises accounting for $2.7B of those losses.
How can you make sure your information (and that of your vendors) are safe? Here are a few tips:

Who’s there?
First and foremost, make sure you know how third-party vendors you work with handle permissions and know their user access protocols. The fewer users with access the better; but more importantly, you want a guarantee that access is secure, with two-factor authentication, frequent password changes and other standard best practices in place.
What’s the plan for a worst case scenario?
Things seem worry-free when no one is trying to take your data, but what security plans do your vendors have in place when a data security incident does occur? These plans should be in writing, and the procedure should include notifying you and any other clients immediately of any data breach. If they can’t tell you their plan for what they’d do in such a situation, can they be trusted in the event it happens?
It’s about more than just security
In today’s day and age it’s not only your data SECURITY that must be a priority; data PRIVACY is just as critical. Have your vendors identified what items within your data necessitate extra security to maintain privacy? What are your vendors’ privacy protocols?
Up-to-date updates
How do your third-party vendors manage their patches, system configurations and penetration testing? A frequent, robust and transparent schedule indicates that they are being proactive about staying on top of things.
Your third-party’s ‘third-party’
Do your vendors undergo third-party compliance verification, or do they handle it in-house?
The known unknowns
New threats are hitting every day, and in new ways. For instance, security breaches launched through older equipment tied into IoT (Internet of Things) networks increased from +15% to +26% in just two years. That may not directly threaten a non-profit….but it may affect other clients that your third-party vendor does business with – which in turn may affect you.
Updated updates
What are your vendors’ policies and practices regarding security? How often are those policies and practices implemented and updated? Who is in charge of that process, and of other compliance issues? Those team members should be a regular part of your interaction with the third-party vendor, and updates should happen proactively – not only when requested, or when a breach has occurred.
Following or making the rules?
While the General Data Protection Regulation (GDPR)’s legislation has affected those who are not currently doing business in the European Union, one thing is for certain: more rules will continue to come from somewhere. Several U.S. states already have data privacy & security laws in effect, even more states have laws currently under debate, and the number of data security bills introduced to Congress has increased in recent years. Ask yourself: is your third-party vendor not only up-to-date, but ahead of the curve?
Is your Board on board?
It is critical for your Board of Directors to be involved in your data security compliance process for several reasons. For one, they need to understand the process and the costs associated with having a solid security plan, as well as the potential cost of being victimized by a data breach. They should consider forming a Risk Management Committee to make the review process part of the Board’s duties. And perhaps most importantly, your Board is likely made up of professionals from different industries, many of which (especially technology, healthcare, insurance and financial services) are far ahead of the curve in dealing with data security. These members may have best practices access to more efficient tools, processes and resources.
Your Data is Secure with DonorPoint
At DonorPoint, we have long-standing protection in place to prevent your sites from being used for fraudulent activity:
- Our network intrusion detection systems scan IP addresses and alert us to traffic coming from suspicious areas of the internet.
- These IP addresses are geo-located, and locations outside of North America and Western Europe are blocked; this functionality is controllable by our partners and clients — in the special case of expected traffic from outside our firewall — via an ‘Enforce Blacklist’ checkbox on all forms.
- Four (4) successive declines from the same IP address results in the address being blocked from subsequent transactions; just as above, this functionality is also controllable by our partners and clients.
We go into more depth in our comprehensive Security and Availability Policy.
If you’d like to discuss your current security situation and see how our software can help your digital security plans, please reach out.
